Running a fast-growing business or a high-stakes real estate firm means you’re spinning a lot of plates. You’re focused on closing deals, scaling your operations, and staying ahead of the competition. Often, the "tech stuff" is something you just expect to work in the background. But here is the reality: as your company grows, so does your target on the back of your network.
Many business owners assume that if they have a firewall and some antivirus software, they’re covered. Unfortunately, the landscape of cybersecurity has changed. Threat actors aren't just looking for big corporations anymore; they are looking for "low-hanging fruit": businesses that have outgrown their basic security setups but haven't yet updated their defenses.
Discover the most common pitfalls we see at Degarmo Technologies and learn how proactive Managed Security Services can bridge the gap between "hoping you're safe" and "knowing you're secure."
1. The "I’ll Patch It Tomorrow" Trap
One of the most frequent mistakes is delaying critical software and system updates. We get it: restarting a server or updating an application can be a nuisance when you’re in the middle of a busy workday. However, unpatched vulnerabilities are the primary gateway for "zero-day" exploits. These are flaws that hackers know about before the general public does, and they move fast.
The Fix:
Stop treating updates as optional. You need a formal patch management process that tracks every asset in your landscape. If you are running legacy systems that can't be patched (like older medical or specialized real estate hardware), those systems must be isolated from the rest of your network. At Degarmo Technologies, we handle this through proactive IT support and management, ensuring your systems stay current without disrupting your workflow.
2. Weak Passwords at the Front Door
It sounds basic, but weak passwords at network gateways remain a massive liability. Using a six-character password for a domain administrator is like locking your front door with a piece of scotch tape. Cybercriminals use automated tools to brute-force these simple codes in seconds.
The Fix:
Explore the power of Multi-Factor Authentication (MFA). It is no longer a luxury; it is a necessity for every internet-accessible point, especially your VPN. Implement strict password policies that require complexity and randomization. If your employees are still using "Password123" or their pet’s name, your network is at risk. We recommend using a centralized identity management system to enforce these rules across your entire organization.
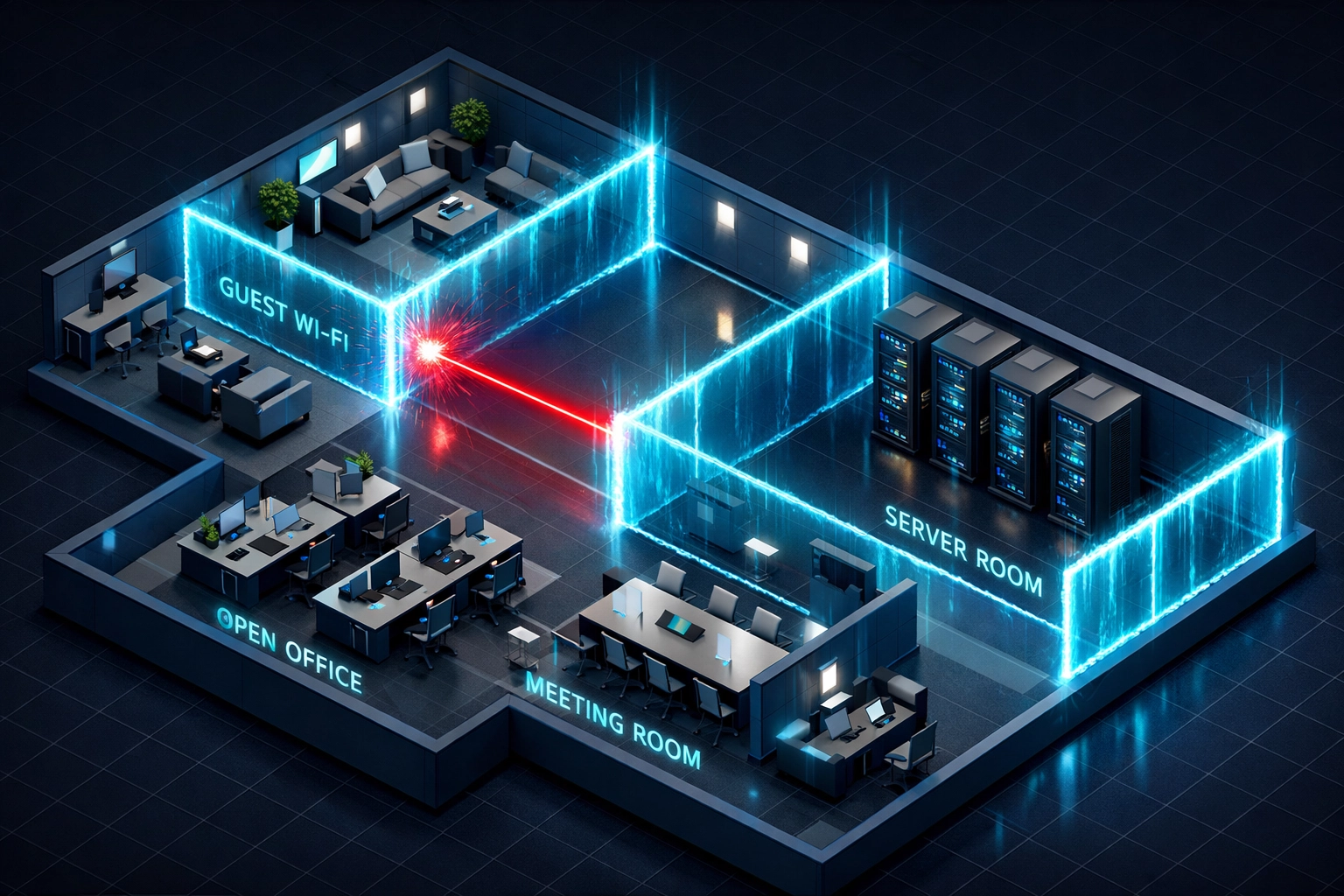
3. A "Flat" Network Architecture
Many small to mid-sized businesses operate on a "flat" network. This means that if a hacker gets into one guest's laptop via the office Wi-Fi, they can move laterally across the entire system until they find your most sensitive financial data or client records. In the real estate world, this could mean a breach in your marketing department leads directly to your escrow files.
The Fix:
Design your network with segmentation. By creating digital barriers between different departments (like HR, Finance, and Guest Wi-Fi), you limit the damage a single breach can cause. Think of it like a modern apartment building: just because someone has a key to the lobby doesn't mean they have a key to every individual unit.
4. Relying Solely on Traditional Antivirus
In 2026, relying only on traditional antivirus is like bringing a knife to a drone fight. Old-school antivirus looks for "signatures" of known viruses. Modern threats, however, use "fileless" malware and sophisticated scripts that don't have a signature. If your antivirus doesn't recognize the file, it lets the threat right through.
The Fix:
Upgrade to Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR). These tools don’t just look for bad files; they look for bad behavior. If a user account suddenly starts encrypting thousands of files at 3:00 AM, EDR recognizes that as a ransomware attack and shuts it down instantly. Our managed security services prioritize these intelligent tools to provide 24/7 protection.
5. Poor Account Hygiene and Privilege Misuse
We often see "Administrator" privileges handed out like candy. If your marketing assistant has full admin rights to your server just because "it was easier to set up that way," you’ve created a massive security hole. If that assistant’s account is compromised, the attacker now has the keys to your entire digital kingdom.
The Fix:
Implement the "Principle of Least Privilege." Users should only have access to the specific data and tools they need to do their jobs. Furthermore, use account tiering. Domain administrators should never log into standard PCs where their credentials can be "cached" and harvested by attackers. Keeping your administrative accounts separate and secure is a hallmark of a professional security posture.

6. Ignoring the "Hidden" Hardware
When people think of network security, they think of laptops and servers. They often forget about the printer in the corner, the smart thermostat in the office, or the IP security cameras. These Internet of Things (IoT) devices are notoriously insecure and are often the "back door" hackers use to enter a network undetected.
The Fix:
Include every single connected device in your security audit. Change the default factory passwords (which are often just "admin/admin") and put these devices on their own isolated network segment. This ensures that even if a smart camera is compromised, it can’t communicate with your primary database.
7. Backups That Haven't Been Tested
The biggest mistake you can make is assuming your backups work just because a light is green. We have seen businesses hit by ransomware only to discover that their backups were also encrypted because they were connected to the same network. Or worse, the backup had been failing for months, and no one noticed.
The Fix:
Follow the 3-2-1 rule: three copies of your data, on two different media types, with at least one copy stored off-site and disconnected (air-gapped) from your network. Most importantly, test your recovery process. An untested backup is just a hope, not a plan. Regular testing can reduce breach costs significantly and ensures you can actually resume operations after a disaster.

Why Integrity and Proactive Care Matter
At Degarmo Technologies, we believe that IT isn't just about fixing things when they break; it's about building a foundation of reliability and integrity. For fast-growing businesses, downtime isn't just an annoyance: it’s lost revenue and a damaged reputation.
Choosing an MSSP (Managed Security Services Provider) means you aren't just buying software; you’re gaining a partner who proactively monitors your network for evolving threats. We take the "IT burden" off your plate so you can focus on scaling your business with the peace of mind that your data, and your clients' data, is protected by industry-leading standards.
Final Thoughts
Network security isn't a one-and-done project. It is a continuous process of improvement and vigilance. By avoiding these seven common mistakes, you place your business in a much stronger position to thrive in an increasingly digital world.
Are you ready to stop worrying about your network and start focusing on your growth? Explore how our tailored IT and Cybersecurity Solutions can protect your future.
Discover the Degarmo difference. Contact us today for a comprehensive security assessment and let’s build a more resilient business together.